About Importance of Data Security in Healthcare in 10 Minutes


In the Health Insurance Portability and Accountability Act of 1996, healthcare data security is stated as essential and mandatory.
To address data security controls, HIPAA Security Rule requires that covered entities (i.e., health plans, health care clearinghouses, and healthcare providers):
- perform a risk assessment
- follow it up with a risk management program
- address any vulnerabilities.
What is data security in healthcare
Generally, data security means securing and protecting data through preventative measures.
To understand a complex topic of HIPAA compliance better, we recommend a read illustrating HIPAA requirements on simple and comprehensible examples.
In healthcare arena, data points include external and internal sources and come from:
- Electronic medical record (EMR)
- Consult notes
- Staff interactions
- CMS (Center for Medicare Services)
- Health plans
- Census from hospitals, etc
On average, patients are estimated to encounter more than 10 connected medical devices in a hospital environment, which reflects how complex and multilayered the process of data accumulation is and what implications it can have if there is a cause for security negligence.
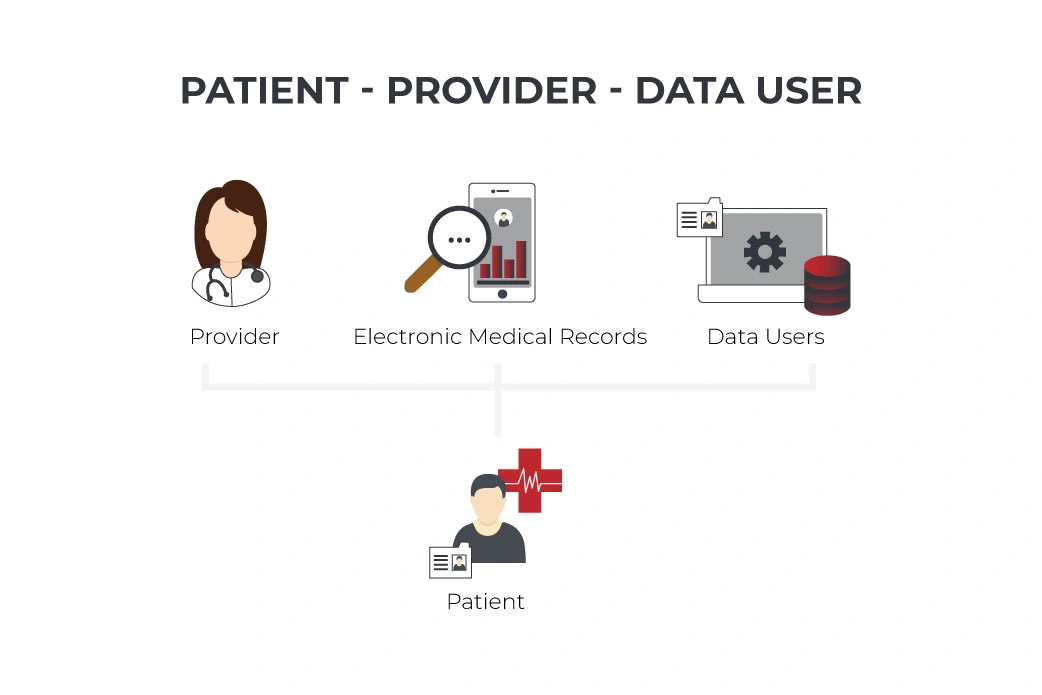
In this context, data security within data management comes to the forefront as it makes a direct impact on quality care, patient engagement, patient outcomes, patient satisfaction, effectiveness of communication, and, obviously, compliance.
Bottom Line: Keeping patient information safe and secure is the top priority of healthcare providers. Hence, the objective of healthcare data security is to come up with a plan that ensures both patient data and healthcare data are protected with the highest level of efficiency.
Violation of standards of healthcare data security
Healthcare data security is determined by healthcare data security standards that are officially codified in HIPAA Privacy Rules.
They determine procedures of management of sensitive patient data incorporating a wide range of legalities from patient tracking, implementing medical devices and data transferring permissions to patients’ and healthcare providers’ financial information.
According to Healthcare Data Breach Report, the healthcare industry suffered from a 25% Increase in breaches in 2020.
Citing the Report further, among the most shocking healthcare data breaches of 2020 was “a ransomware attack on the cloud service provider Blackbaud Inc. The actual number of records exposed and obtained by the hackers has not been made public, but more than 100 of Blackbaud’s healthcare clients were affected and more than 10 million records are known to have been compromised”.
Verizon Report provides even more alarming statistics: according to their findings, data breaches with the prevalence of crimeware and privilege misuse increased by 58% in 2020.
Among the threat actors, there is almost equal distribution between externally caused ones that reach 51% and the internally caused (48%).
Bottom Line: Violation of standards of healthcare data security falls under legal prosecution. Depending on the severity of data security breach, the punishment can result in heavy fines and criminal charges.
The situation with big data security and privacy issues in healthcare results from emerging data security threats in healthcare.
One of the reasons for concern is related to the fact that medical devices get more connected, which imposes higher risks on patient data management.

The past decade has seen the rapid development of measures to ensure healthcare data security in the US, UK and other European nation states. Below, we will discuss what are some ways to maintain security of health information in these countries and what is the difference between approaches they take.
Data security in healthcare in the US and Europe
US data handling and protection policies do not apply a ‘citizen first’ approach.
However, HIPAA Act makes it mandatory that healthcare organizations and companies that deal with protected health information (PHI) take physical, network, and process security actionable steps for delivering healthcare services and providing safe treatment and payments.
The Health Insurance Portability and Accountability Act (HIPAA) has a rich chronological history and roots in 1996. It constantly widens and updates the definitions of protected health information that currently include demographic information, patient personal and contact information, residence, medical record number, social security number, and any identity-related data.
Unlike the US, Europe practises a unified approach to healthcare data protection. In the EU and UK, data security procedures are determined by Data Protection Directive that is universally applicable across any industry and business sector.
It implies that the collection of personal data is ruled by strict legal norms and must be justified by specific purposes not violating healthcare consumers’ rights.
Thus, a major difference between the legislation in the United States and the EU when it comes to data protection or data security in healthcare is the approach to securing data.
As for Europe, this approach is more solidified since the legislation is the result of the joined efforts of all member states to ensure that national standards are the same. Data Protection Directive is the basis for further implementation on the level of national legislation.
By contrast, a single, universally applicable privacy law does not exist in the USA. Data protection is exercised on a federal level and state levels, which means that electronic media and PHI transfer, removal, disposal, and reuse restrictions on healthcare data can vary.
Bottom Line: In the US and Europe an individual’s personal information can be collected, shared, and accessed exclusively in a transparent and trusted manner. Businesses including healthcare organizations cannot operate if they do not follow guidelines for compliance and certification of their activities in regard to healthcare data security and protection.
It highlights data security in healthcare as a growing issue, and below, we discuss the biggest challenges and their causes in healthcare.
Healthcare data security challenges, risks and issues
What is the biggest threat to the security of healthcare data?
It is not a trivial question because as far as cyberattacks occur, the healthcare industry continues to be a target of choice.
If we take a deeper look at this problem, we can see that mostly challenges, risks and threats come to the issues in the following domains:
Device connectivity malfunction
Our dependence on devices and software in healthcare makes us vulnerable to virus attacks, malware and hacking. The safety of patients can be also threatened by connection failures and incoordination of multiple types of devices. For instance, the device can become unresponsive due to malfunction at the critical moment, or connected devices can fall short of alignment due to differences in routine updates.
Therefore, the healthcare industry is forced to adapt to new and more stricter security measures to claim protection of sensitive patient data and exclude unsafe practices.
Poor cyber inventory
The lack of knowledge about the systems in a specific healthcare organization can result in missing or overlooking the security issues. Failures on the level of network observance are likely to create situations that could be described as prerequisite to harm.
Enumeration of networks and identification of data security vulnerabilities in healthcare connected devices and computerized maintenance management systems are the basic measures to mitigate risks. Additionally, the proper inventory will also help identify outdated and unsupported devices.
Vendor lock-in risks
The vendor lock-in becomes a serious problem when the offered solutions do not meet the data security standards and create risks for patient information privacy. Hence, healthcare providers are advised to choose vendors who are ready to be in charge of security risk assessment and provide a full cycle of management service when it comes to identifying medical device security issues.
Complexity of healthcare data security testing
The problems that stem from data security testing are mostly associated with complexity of processes and procedures that may include actual data collection, review of gathered data, analysis, vulnerability estimation, adjustment of the security systems to provide a stronger protection of privacy and confidentiality of patient data. Increasing complexity can be overwhelming and block adequate protection measures rather than encourage building strong data security policies.
Bottom Line: Primarily, negligence of privacy issues in healthcare causes data security breaches that bring considerable financial and reputation losses to healthcare organizations.
Overall, top threats and challenges relate to:
- privacy and confidentiality
- lapses in security
- usage of outdated software
- risks associated with authenticity of identification and reidentification
- liabilities for providing inadequate patient information
- connectivity and device coordination issues
- bias of algorithms that can make a negative impact on outcomes
Besides, healthcare providers experience tensions over data sharing and trustworthiness of AI-powered tools.
In what ways can healthcare organizations ensure that they have sound data security protocols in place? To initiate a healthcare data security plan and introduce it successfully, we consider some actionable steps that healthcare businesses can take today.
3 top actionable steps to protect patient data
Evidently, sharing the information now goes much faster than we can handle if we use manual systems of management and security. Among the top measures that can ensure healthcare data protection, there are the following:

Annual risk analysis
To secure healthcare data security and ensure data protection, it is important that all the stakeholders pay attention not only to IT-related issues but to analysis of spending and allocation of resources (for example, consideration of privacy filters, security hoods, etc.) for accurate assessment of probable risks. Implementing the practice of risk assessment at least annually can elevate data security to a new level.
Encrypted data
With a decryption key and the fully implemented encryption process that implies scrambling of readable text, healthcare providers can ensure protection of patient data being sent, received, and stored.
Compliant software
With robust end to end solutions, healthcare providers can combat emerging risks in healthcare data protection and build a healthcare data security policy for prevention of breaches.
As it was mentioned above, aside from challenges associated with hacking and intentional attacks to compromise data security, sometimes no malice can be intended but still the data breach can take place with detrimental consequences. It concerns cases of software malfunction.
The best way to secure it is to deploy healthcare software development service that provides designing a system initially featured with options to diminish data security issues.
With a bigger number of patient portals and introducing new interaction channels with their patients, healthcare providers come across attacks on web applications. It is a reason for attacks on web applications to be among the most common.
As one of the healthcare data security solutions, there can be the implementation of bespoke HIPAA compliant healthcare CRM as the measure of protection of patients and healthcare professionals against probable data misuse and cyberattacks.
Applications that are subject to security risk assessments are identified, assessed, and implemented. Furthemore, taking this approach aims at identifying application security flaws at the stage of design and development.
It enables healthcare providers to get apps that have reliable risk assessment functionality and allows healthcare businesses to see the application from the point of view of a potential attacker and, thus, prevent failures.
Conclusion
It is now time for healthcare providers on all tiers to revise their HIPAA compliance policy and build proper strategies to collect, access and share sensitive information securely.
Since a key element of the Health Insurance Portability and Accountability Act rules is the security of healthcare data, you can save time and effort by contacting our experts to learn more about solutions for healthcare data security.
Build your ideal
software today