Comprehensive Security Assessment Services
We are currently in the era of AI and auto-generated code, so security incidents and breaches are bound to happen more often. Our assessment helps you get clarity and control over cybersecurity risks: where you’re vulnerable, how serious the risks are, and what exact steps to fix first.
Business First
Code Next
Let’s talk
Built for companies that handle real data
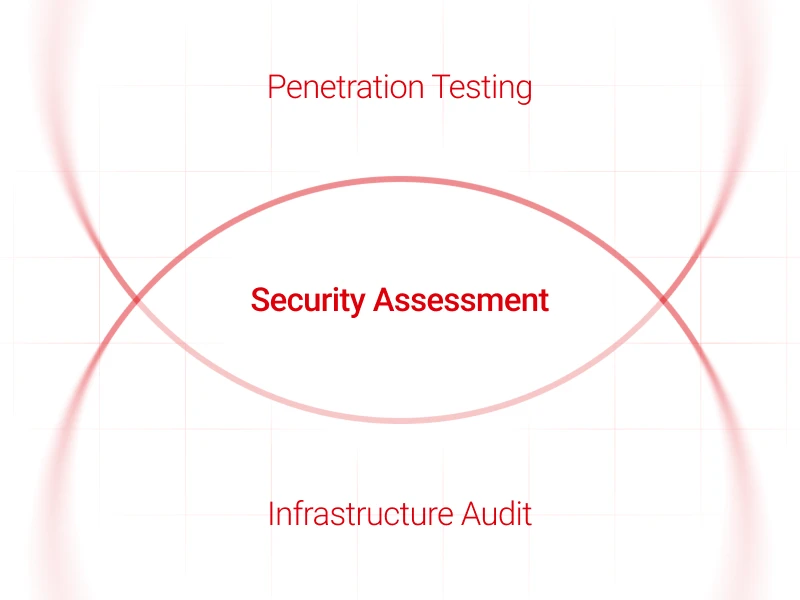
Our Comprehensive Security Assessment includes penetration testing and an infrastructure audit. Together, they review your systems, environments, and code through practical security testing and configuration-focused analysis — so you can move from reacting to security issues toward more continuous protection.
When to run a Security Assessment
A breach occurred
A security breach has already happened and you need someone to fix it and make sure it does not happen again.
Growth with higher security requirements
As you scale and work with more demanding partners, a proven level of security or an official certification may be crucial.
Credibility without in-house security
You want to build credibility with partners and customers but have no expertise or experience in security precautions.
What we assess
This assessment includes penetration testing and infrastructure audit. It also covers web application & API penetration testing and a source code audit as part of the engagement.

Penetration Testing
An authorized, simulated cyberattack on your organization’s IT systems to identify and fix vulnerabilities before actual hackers can exploit them. Unlike basic automated scans, it combines automated tools and manual techniques to probe for weaknesses in your defenses.
To increase efficiency and coverage, we leverage AI-assisted tools for selected testing activities in a controlled manner.
Think of it as: “How vulnerable is our system right now?”

Infrastructure Audit
A specialized, deep-dive review of your IT environment (servers, networks, cloud setups, and databases) to assess how the underlying technology is configured and operating.
While a security audit looks at policies, an infrastructure audit focuses on the health, configuration, and resilience of the actual systems, helping identify insecure settings, excessive permissions, and exposed services across the environment.
Think of it as: “Is our technology built and configured correctly?”
What Comprehensive Security Assessment includes
Information Gathering
Collect publicly and internally available information about systems (domains, IPs, technologies, exposed services).
Building DFD
Create a visual representation that maps how information enters, travels through, is processed, stored, and exits a system—to help identify vulnerabilities, analyze data pathways, and ensure compliance.
Automated Vulnerability Scanning
Use tools to identify known weaknesses such as outdated software, misconfigurations, or missing patches.
AI-Assisted Tooling
Leverage AI-assisted tools to accelerate certain testing activities, used in a controlled manner and configured to avoid transmitting source code, sensitive data, or proprietary information to external AI services.
Web Application & API Penetration Testing
Simulate real-world attacks to identify vulnerabilities in web applications and APIs before malicious actors can exploit them.
Source Code Audit
A comprehensive, line-by-line analysis of software code to identify security vulnerabilities, bugs, performance bottlenecks, and compliance violations.
Impact Assessment
Analyze what data could be accessed, modified, or destroyed.
Network Architecture Review
Analyze network design, segmentation, firewalls, and exposed services.
Cloud Configuration Review
Examine cloud resources (AWS, Azure, GCP, etc.) for insecure settings, excessive permissions, and public exposure.
Server & System Configuration Review
Check operating systems, patch levels, services, and hardening settings.
Access Control Analysis
Review who has access to what, and whether permissions are excessive.
Backup & Disaster Recovery Checks
Verify if backups exist, are protected, and can realistically be restored.
Vulnerability Scanning
Scan infrastructure components for known weaknesses and outdated software.
Secrets Management
Identify hardcoded secrets (API keys, tokens, passwords, certificates) and how secrets are stored, accessed, rotated, and protected across infrastructure, codebases, and CI/CD pipelines to prevent unauthorized access and leakage.
Supply Chain Security
Evaluate third-party dependencies, images, and build pipelines to identify risks from vulnerable, malicious, or improperly managed external components.

Business First
Code Next
Let’s talk
How Security Assessment works
Systems & Data Flow Discovery
We identify the systems in scope and collect key information about them (domains, IPs, technologies, exposed services). We also build a Data Flow Diagram (DFD) that maps how information enters, travels through, is processed, stored, and exits the system.
You receive: a clear view of what is being assessed and a DFD that supports vulnerability identification and data pathway analysis.

Vulnerability Scanning + Attack Simulation
We run automated vulnerability scanning to identify known weaknesses such as outdated software, misconfigurations, or missing patches. We also perform web application & API penetration testing by simulating real-world attacks.
You receive: identified weaknesses from scanning and vulnerabilities found through real-world attack simulation in web applications and APIs.

Source Code + Infrastructure Audit
We conduct a source code audit with line-by-line analysis to identify security vulnerabilities, bugs, performance bottlenecks, and compliance violations. In parallel, we perform an infrastructure audit of servers, networks, cloud setups (if applicable), and databases, including network architecture review, access control analysis, backup & disaster recovery checks, secrets management, supply chain security, and infrastructure vulnerability scanning.
You receive: code-level and infrastructure-level findings based on how your systems are built, configured, and maintained.

Impact Assessment
We assess what data could be accessed, modified, or destroyed based on the identified vulnerabilities.
You receive: an impact view tied to the findings—focused on what could be affected.
Detailed Report & Recommendations
We deliver a detailed report with a clear explanation of vulnerabilities, their severity, and exact steps to fix them.
You receive: a remediation-ready deliverable your team can use to address issues in a structured way.

Apply Fixes Based on Recommendations
You use the report’s recommendations to address identified vulnerabilities and reduce security risk across systems, infrastructure, and code.
You receive: a clear set of exact fix steps to implement and a structured basis for ongoing security improvements.

Business First
Code Next
Let’s talk
If you want clarity on where you’re vulnerable, how serious the risks are, and what to fix first, request a Comprehensive Security Assessment.