What is Data Compliance? Top Things To Know About HIPAA, GDPR, PIPEDA

Complying with various regulations and standards (i.e. medical data, billing information, customer base, etc.) for the privacy, accessibility and integrity of regulated data is known as data compliance.
Why did it become so important? Due to a boom in technology, customers feel concerned over the lack of transparency in data collection as well as data abuse and illegal usage. Legislators responded to privacy issues by promoting a variety of data privacy frameworks and imposing them on businesses.
Top Data Privacy Frameworks
Some of the most noteworthy laws and regulations for ensuring data security, which have been established by governments across the globe, include:
HIPAA
GDPR
PIPEDA
CCPA.
These privacy frameworks are mandatory in implementation in private and public sectors. Since their main aim is the focus on the privacy policy in business practices, it is necessary to be familiar with these privacy laws to best comply with data regulations.
They stand for:
the Health Insurance Portability and Accountability Act (HIPAA)
the General Data Protection Regulation (GDPR)
the Personal Information Protection and Electronic Documents Act (PIPEDA)
the California Consumer Privacy Act (CCPA).
While there are many differences among four frameworks, all of them are to protect the right of users to manage and control their data.
Below, we discuss:
what basics stand behind the titles
what regulations they imply
how they are applicable to businesses
how these regulations differ from each other.
HIPAA: Regulated Data, Expected Changes
HIPAA was enacted in 1996. It is the only US federal rule that protects healthcare customers by limiting access to sensitive information and imposing penalties for data breach and rules violation. In practicality, it legally provides privacy for health-related data.
Any organization that is involved in the healthcare industry is required to follow HIPAA compliance standards.
In particular, they imply the following:
There are four sources of regulated data, healthcare providers, health plans, healthcare clearinghouses, and business associates (According to recent HIPAA rules, businesses associate can be defined as a person, entity or a service that is involved in the disclosure of PHI, which makes software companies allowed with the access to ePHI a subject of the named regulations).
The act specifies the uses and disclosures of personal health information identifying the person.
As mentioned above, PHI (Protected Health Information) is specifically regulated by this law, and anyone with access to it is subject to it.
This act assists patients in accessing, updating, and transferring their healthcare information.
To ensure compliance with HIPAA regulations, a Privacy Officer and a Data Security Officer are required to be appointed.
Organizations are required to inform the public of a data breach within 60 days, according to the HIPAA Regulations.
Notification may be an annual affair if there are fewer than 500 individuals affected.
Business practice under HIPAA implies that billing information and payment data must be protected against being disclosed to any third party. The same goes for confidentiality of patient information (i.e., it must be accessible only to healthcare customers and in case of sharing, the user consent for processing the information by outsiders is required).
HIPAA specifies that entities are to organize the procedure of Risk Assessment of HIPAA Compliance yearly.
In 2022, certain HIPAA amendments are expected to be introduced. For instance, while currently HIPAA rule demands that a patient should get the response about a PHI request within 60 days, the proposed rule will reduce the response time to 30 days.
HIPAA Compliance Checklist
To be HIPAA-compliant, businesses are strongly advised to consider the following steps:
Establish points of control for accessing data including regular and emergency cases use. Aside from the protected user login information, there must be a secure protocol that provides access to ePHI under force majeure.
To ensure HIPAA Compliance, utilize the expertise of an appointed Privacy and Security Officer for full data protection.
One of the key responsibilities of a Privacy Security Officer is employee training: make sure that employees’ knowledge of HIPAA policies is evaluated and well-documented.
Get prepared for yearly audits that are legally required in your business niche.
Upon conducting checkups and audits, put down all the results for identifying the areas of data privacy improvement.
Create a plan of implementation of the amendments.
Keep the information on improvements updated.
GDPR: Regulated Data
GDPR is the European Union (EU) and European Economic Area (EEA that includes Iceland, Lichtenstein, and Norway) law that was enacted in 2018 which stems from directives of 1995 and 1998 with regard to definition of personal data and its protection.
The law of 2018 states it is mandatory for businesses to provide measures of privacy in collecting and handling user personal data. In particular, it means:
Regulated data concerns the information that identifies a person including the name and any contact number and residence address.
GDPR defines Protected Health Information (PHI) and personally identifiable information (PII) as the subject of relulation.
Data collected in marketing including recent purchases and online actions, if it involves a person’s identification falls under the definition of regulated data too.
Customer data can be obtained only with the permission from the customer.
In case the user wants to know how exactly the data is collected, the party gathering the info must be ready with an easy to understand explanation of the data collection process. Besides, there must be an option for erasing the collected data.
GDPR Regulation engages two agents, data controllers(those that process personal data directly, legal person, body or authority) and data processors(those that process personal data on behalf of the named data controller).
EU citizens are entitled with the right to be fully informed about privacy policies, delete data, download it and annule consent on data collection.
In case of data violation or data breach, GDPR Regulation requires to notify the user within 72 hours.
The organization dealing with regulated data must have a Data Protection Officer (DPO) responsible for monitoring GDPR compliance and data management.
DPR Compliance is applicable even if data processing of EU subjects occurs in a third country.
GDPR specifies that entities are to organize the procedure of Data Protection Impact Assessment (DPIA) every 3 years except for cases when immediate actions are required (for example, if data collection creates specified high risks to customers).
2020 became the year of several cases when big companies suffered huge financial losses due to proven data breach. It resulted in penalties and reputational losses: Facebook was fined £500 000 in Cambridge Analytica scheme when data of 87 million users was breached in sharing.
GDPR Compliance Checklist
To be GDPR-compliant, businesses are strongly advised to consider the following steps:
Assign monitoring role to DPO (Data Protection Officer) and organize staff training in GDPR policy compliance accordingly.
Have a comprehensive list of data points collected within business activities.
Identify common and high risk activities and address any security and prior issues prior to running Data Protection Impact Assessment.
Check legalities concerning user consent. Additionally, remember that obtaining consent of users under 18 is impossible without the authority of a guardian.
If there are special rules implied by certain member states additionally relevant to your business, make it mandatory to include them into your policies.
Be precise with the users when it comes to data collection and transfer.
To prevent data breach and violations of regulation, track the transfer process for additional protection of personally and financially sensitive information.
PIPEDA: Regulated Data
In Canada, organizations related to a private sector are to comply with the Personal Information Protection and Electronic Documents Act (PIPEDA) that was enacted in 2001. Recent amendments about responsibilities for data breach were passed in 2018.
PIPEDA regulates business practice in the domain of gathering data so that customer privacy concerns could be addressed successfully.
Any business that falls under the jurisdiction of federal regulation in Canada must comply to PIPEDA when it comes to:
gathering personal data
distributing it within business operations and activities.
PIPEDA compliance implies the following:
Users are entitled to know the purpose of sharing their data
Users can demand their data storage information
Users should be informed on the legal actions in case their privacy rights are violated
Personal information definition is rather wide as it encompasses name, demographics, any ID number, medical record, income numbers, work records, and employment details, legal status, family status, and financial details including loans and credits.
To use personal data, businesses must obtain an explicit consent for collecting and sharing the information further.
A company can be fined up to $100,000 for each time it violates PIPEDA requirements with intention.
It is a requirement that Parliament conducts a review of the Personal Information Protection and Electronic Documents Act (PIPEDA) every five years.
PIPEDA Compliance Checklist
According to PIPEDA, personal information is “information about an identifiable individual.” Since this definition embodies a broad range of notions, businesses are strongly advised to consider the following steps to be PIPEDA-compliant:
Follow the rule of ‘reasonable collection’ that implies that you gather the information determined by specific purpose and not beyond it.
Initiate personal information protection by stating it in your business privacy policy.
Inform users in an easy to understand manner on their data usage and offer the options of data management.
If you are an employer, you are entitled to restrict access to business-related information without special authorization.
As an employee, you are entitled to have access information directly related to your job description.
Keep your privacy policies updated.
Provide your business with technological means of data control.
Although PIPEDA does not specify a strict time limit on notifications for data breach notification to individuals, it suggests that businesses must report serious data compromise and data loss to the Privacy Commissioner of Canada as soon as possible.
CCPA: Regulated Data
In 2018, California Consumer Privacy Act (CCPA) was enacted for regulation of processing and movement of user data.
In 2020, Californians voted for the California Privacy Rights Act (CPRA), which brings more specifications to the CCPA. It will be enacted on the state legislation level in 2023.
Since CCPA gives a broad definition of businesses that are subject to the act regulations, most tech companies are to comply with the law. In particular, such business giants as Microsoft, Samsung, Apple, Facebook, and Amazon fall under CCPA compliance.
CCPA implies:
This privacy act is applicable to user bases exceeding 50 000 customers, devices and households. It also applies if the revenue of the business counts over $US 25 million annually.
It’s important to note that the CCPA applies to all businesses and entities that collect data from Californians and, thus, it is equally mandatory for businesses to be familiar with CCPA legal norms whether their headquarters are located within or outside California.
Furthermore, businesses with a customer base of over 4 million users are specially categorized with extra responsibilities under the stated privacy act.
According to legal norms of this privacy act, personal information of the user includes: names, contact numbers including Email, IP addresses, demographics, finance-related information, passwords, account names, browsing history, geolocation in any given time, login data.
Residents of California expect to know all the data collection procedures and are to be provided with options for deleting their information, evaluating it as discriminatory, and being notified every time their information is gathered.
Consumers now can start administrative proceedings over privacy concerns: violation of data protection can be punished with fines starting with $2,500 for each case of data breach.
CCPA Compliance Checklist
To be CCPA-compliant, businesses are strongly advised to consider the following steps:
Take actions when it comes to providing cybersecurity of consumer records.
Make regular audits and build privacy strategies to enhance protection.
Train the business staff for impeccable knowledge of privacy policies. In particular, ensure that your employees know where to send privacy-related questions and what business department is in charge of data management.
Be transparent in data processing and do not go beyond the minimum in data collection.
In case data collection implies monitoring, tracking or surveillance of any kind, it can potentially involve the usage of sensitive information. Therefore, the consent permission and agreement regulations must be strictly observed.
Similarities and Differences: HIPAA vs GDPR vs PIPEDA vs CCPA
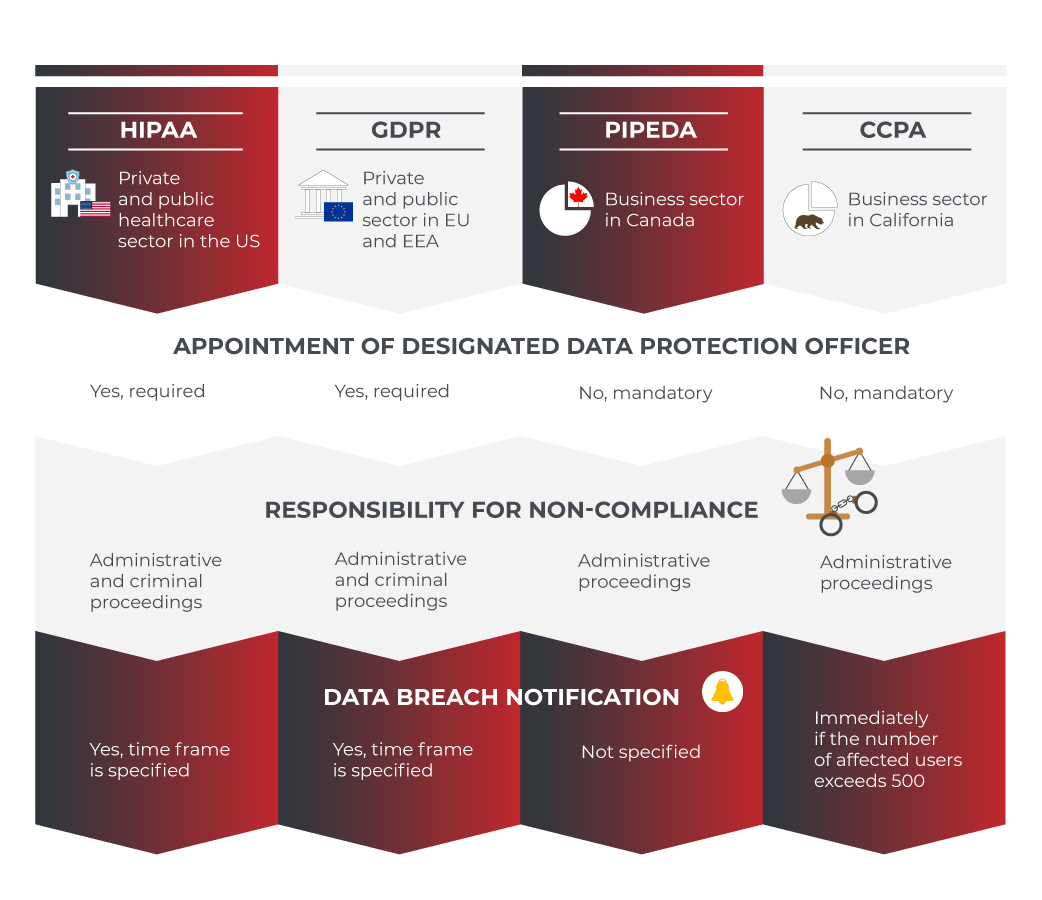
Compliance points HIPAA GDPR PIPEDA CCPA Applicable to Private and public healthcare sector in the US Private and public sector in EU and EEA Business sector in Canada Business sector in California Appointment of designated data protection officer Yes, required Yes, required Not mandatory Not mandatory Data breach notification Yes, time frame is specified Yes, time frame is specified Not specified Immediately if the number of affected users exceeds 500 Responsibility for non-compliance Yes, administrative and criminal proceedings Yes, administrative and criminal proceedings Yes, administrative proceedings Yes, administrative proceedings |
Conclusion
To best ensure compliance with data regulations, it is important to become familiar with some of the key points of international data privacy laws.
To avoid penalties, businesses are advised to take preliminary steps in providing privacy protocols.
In particular, it would be helpful to restrict the parameters of personal information to a minimum. Any information point should be justified by an easy to understand objective.
It will assist in creating transparency for your customers and facilitate obtaining user consent.
Following the key rules of accountability and accuracy in business operations by limiting use of personal data, organizations will be able to maintain the safeguards of privacy and face challenges of compliance without fail.
Clear privacy policy and legally implemented cybersecurity protocols provided by professional services like CodeIT with regard to what information can be disclosed in data collection helps companies to be compliant to most noteworthy regulations.
Build your ideal
software today